Open Source Intelligence Gathering
Requirements:
1. SPIDERFOOT - Download2. WINDOWS 10
3. PYTHON (I prefer ANACONDA) - Download
STEP 1:
Download the open source version of Spiderfoot from the above given link.
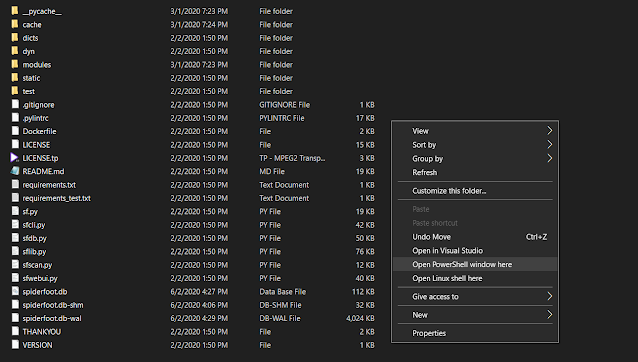
(SHIFT + Right Click) to get the power shell option in menu.
STEP 2:
Open PowerShell and type the following commands
Case 1: If you are using just python
pip3 install -r requirements.txt
Case 2: If you are using Anaconda ( my case )
pip install -r requirements.txt --user
STEP 3:
Once its done installing all the dependencies, execute the following command to start the web interface-
python sf.py -l 127.0.0.1:5001
Now open any browser and open http://127.0.0.1:5001
STEP 4:
Adding up API keys. To get the API key you need to register in the given service and get the API key.
Paste the API key into relevant box and click on SAVE.
The more API keys you will add the more detailed output you will get. ☺
STEP 5:
Starting a Scan. Go-To the New Scan tab and provide the details of the target. You can select all the modules or just do module specific scan.
CLICK on SCAN





Comments
Post a Comment